CVE-2026-36358 PoC - Juzaweb CMS v.5.0.0(XSS)
CVE-2026-36358 PoC - Juzaweb CMS v.5.0.0 (XSS)
漏洞描述:
Juzaweb CMS 5.0.0 版本在 /admin/banner-ads 组件中存在存储型跨站脚本(XSS)漏洞。已认证的管理员可以将任意 JavaScript 代码注入到“HTML”类型的广告内容(Body)中。当任何用户(包括未认证的访客)访问网站首页时,该恶意脚本将在其浏览器中执行。
受影响产品: Juzaweb CMS
受影响版本: 5.0.0
漏洞类型: 存储型跨站脚本(XSS)
漏洞验证(PoC):
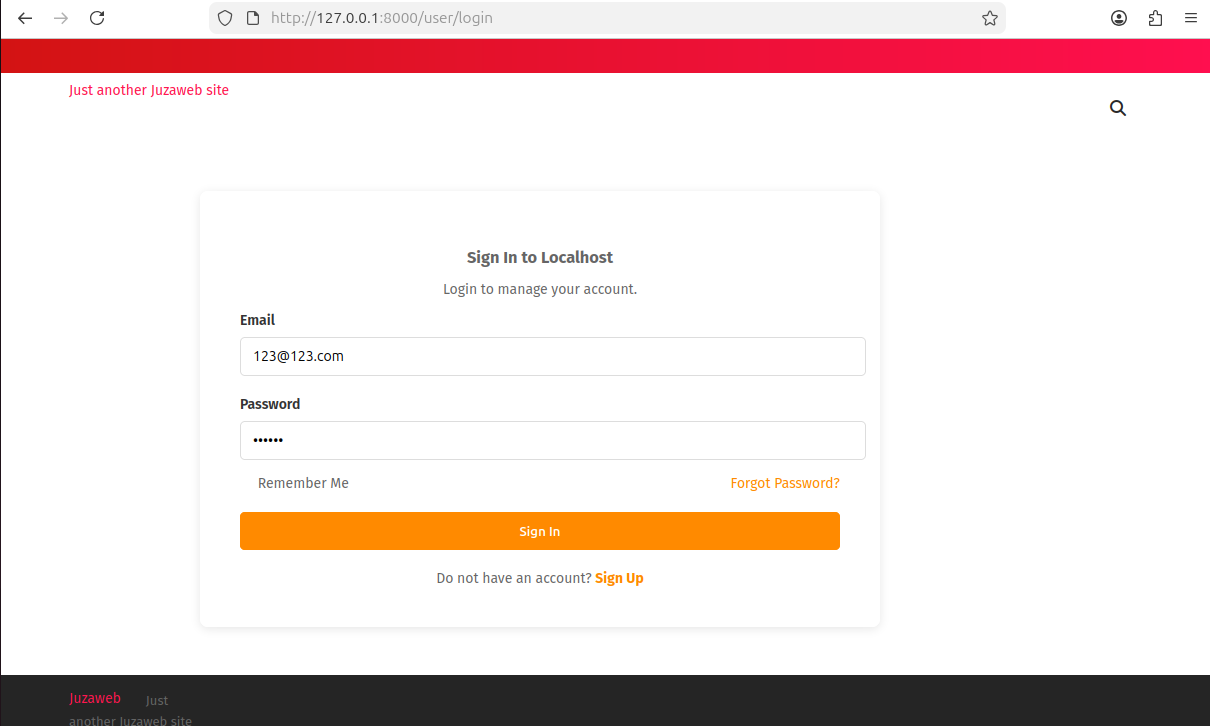
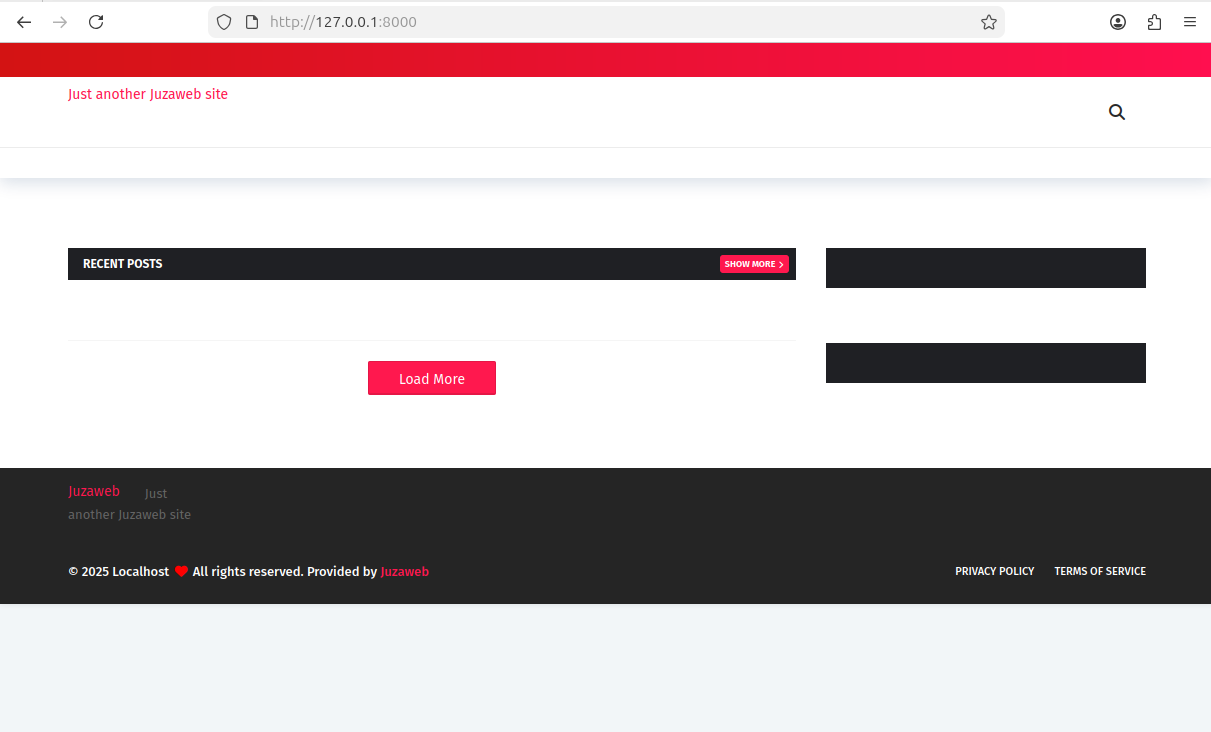
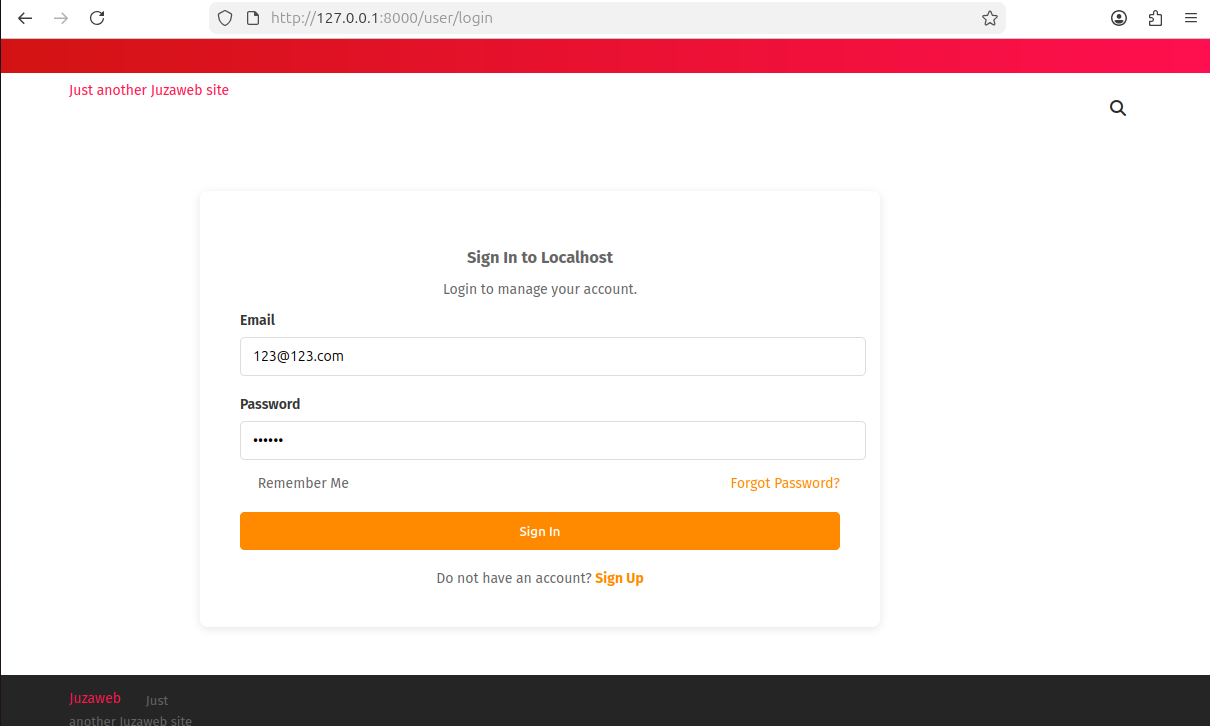
首先是正常搭建和注册平台,这里我注册的管理员账密为123@123.com/123456 搭建好平台后可以看到网站页面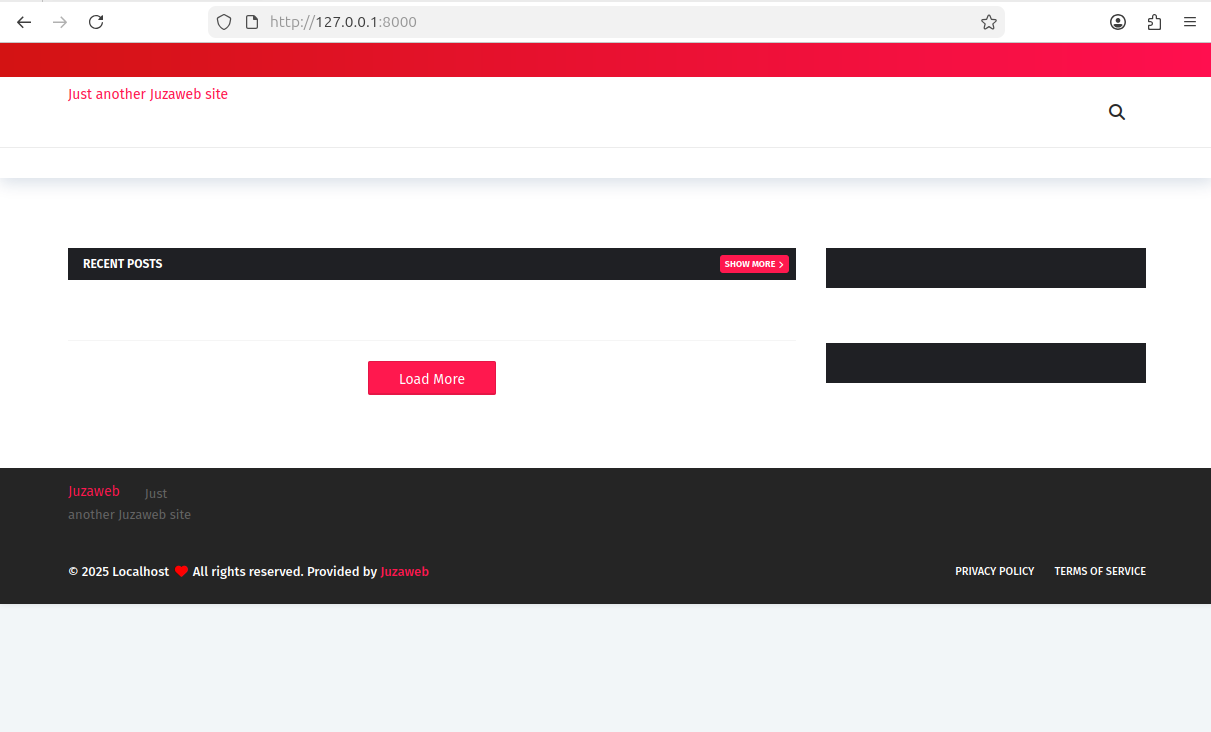 访问/admin并登录
访问/admin并登录
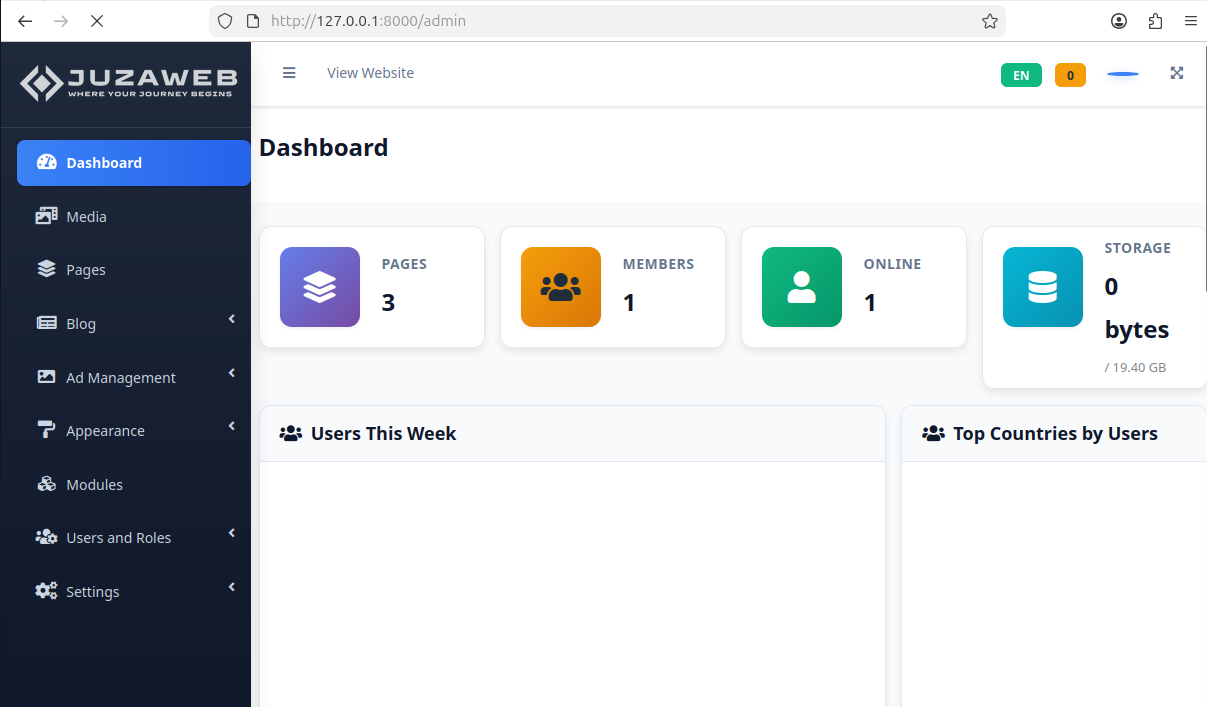
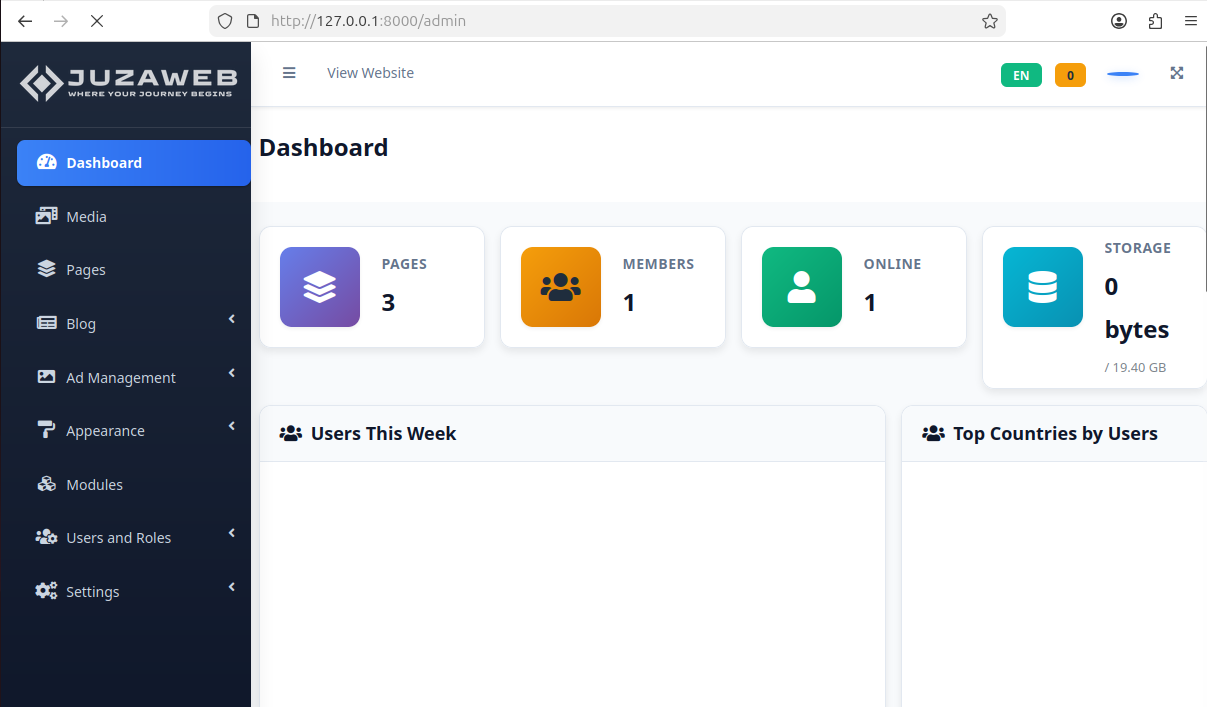
 登录后即可进入admin后台管理
登录后即可进入admin后台管理
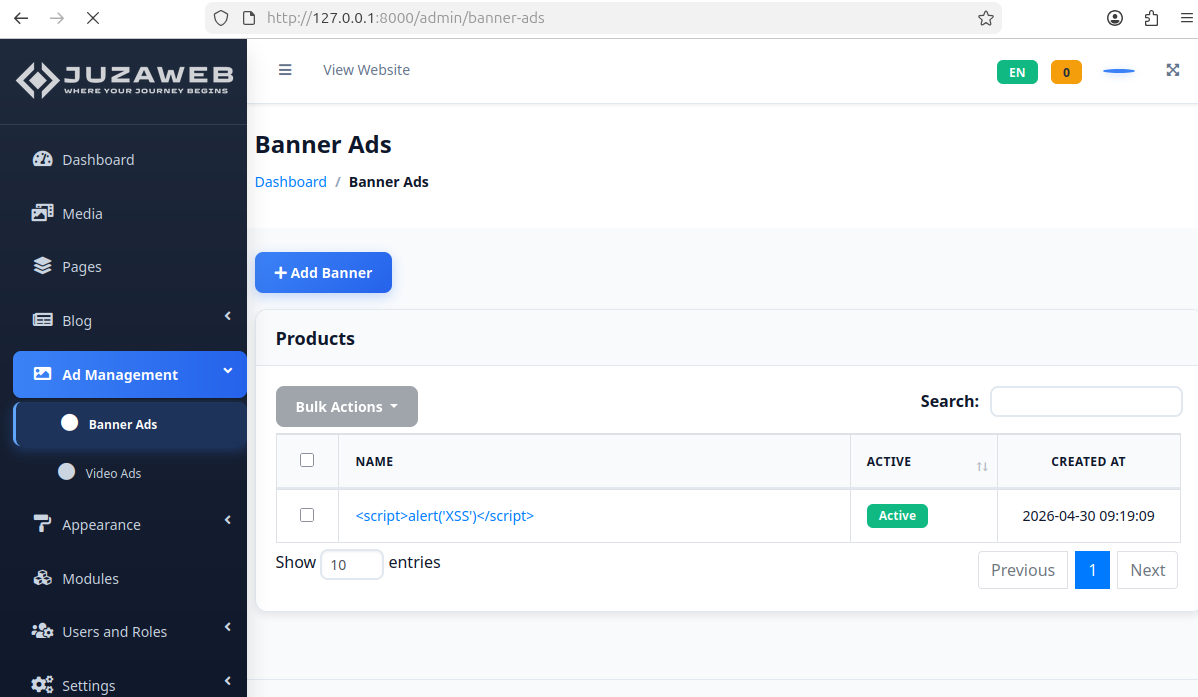
 访问/admin/banner-ads路由,点击添加Add Banner进入创建广告页面
访问/admin/banner-ads路由,点击添加Add Banner进入创建广告页面 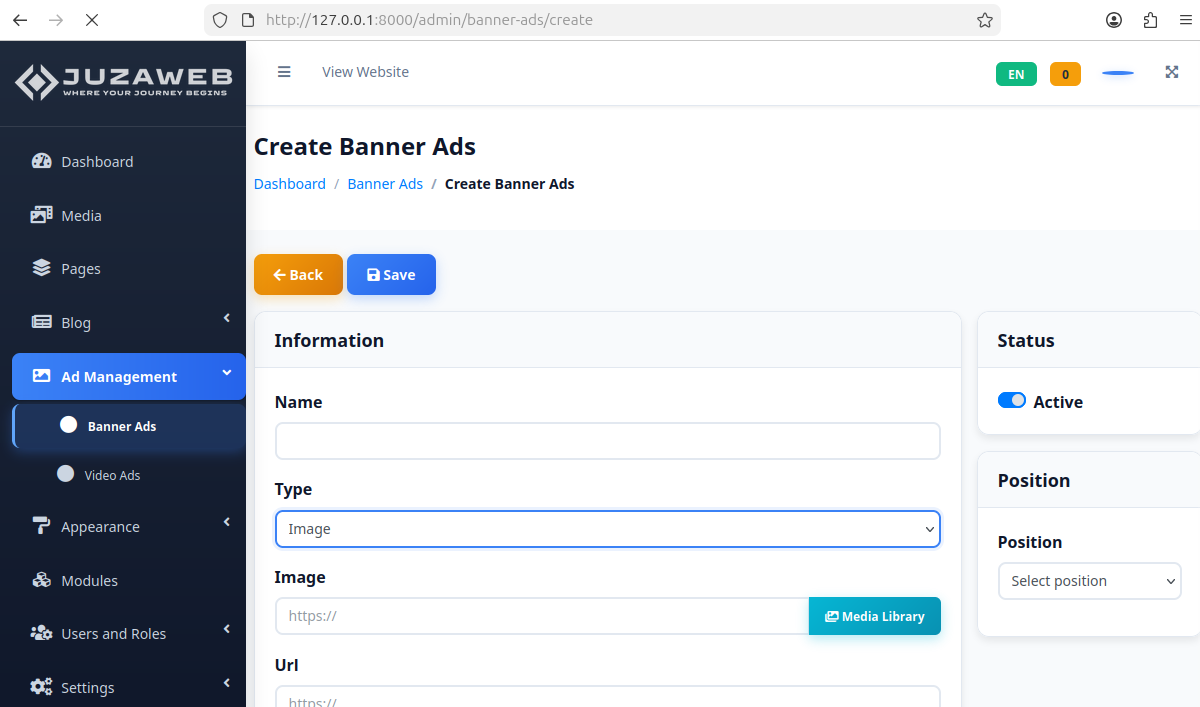 Type改为HTML格式,Body填入恶意XSS代码
Type改为HTML格式,Body填入恶意XSS代码 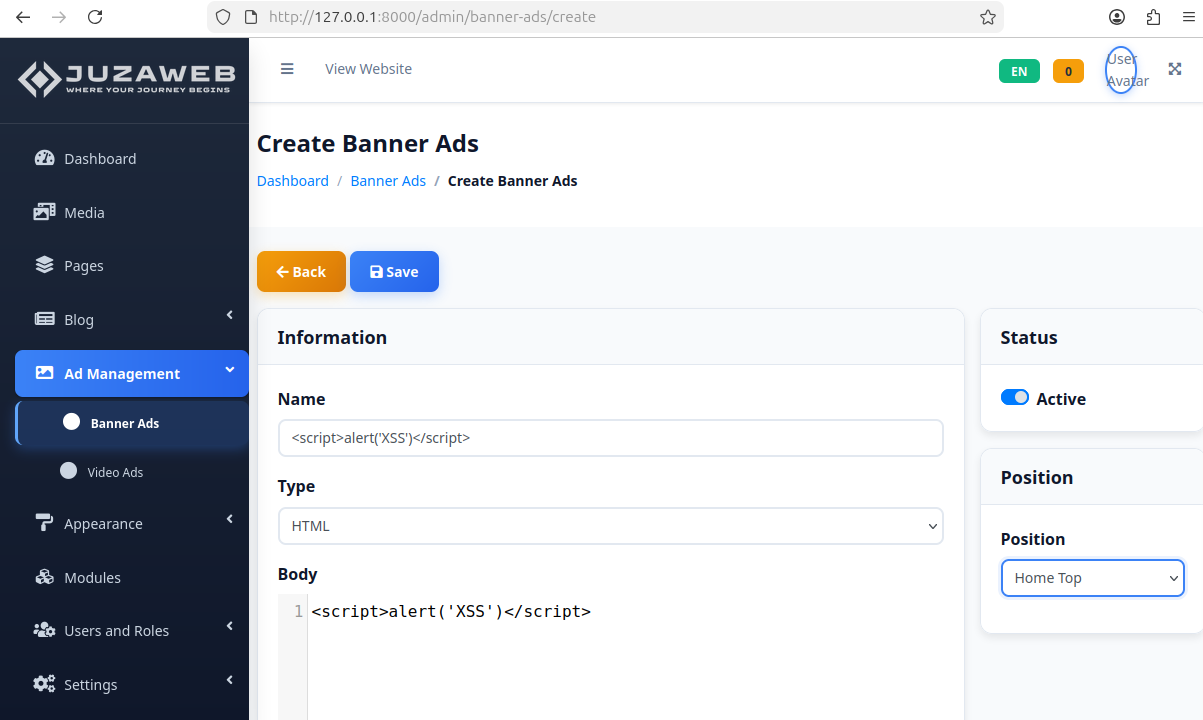 如果提示这样的错误
如果提示这样的错误
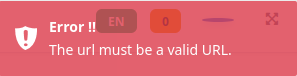
请返回Image Type在URL那一栏随便填一个url 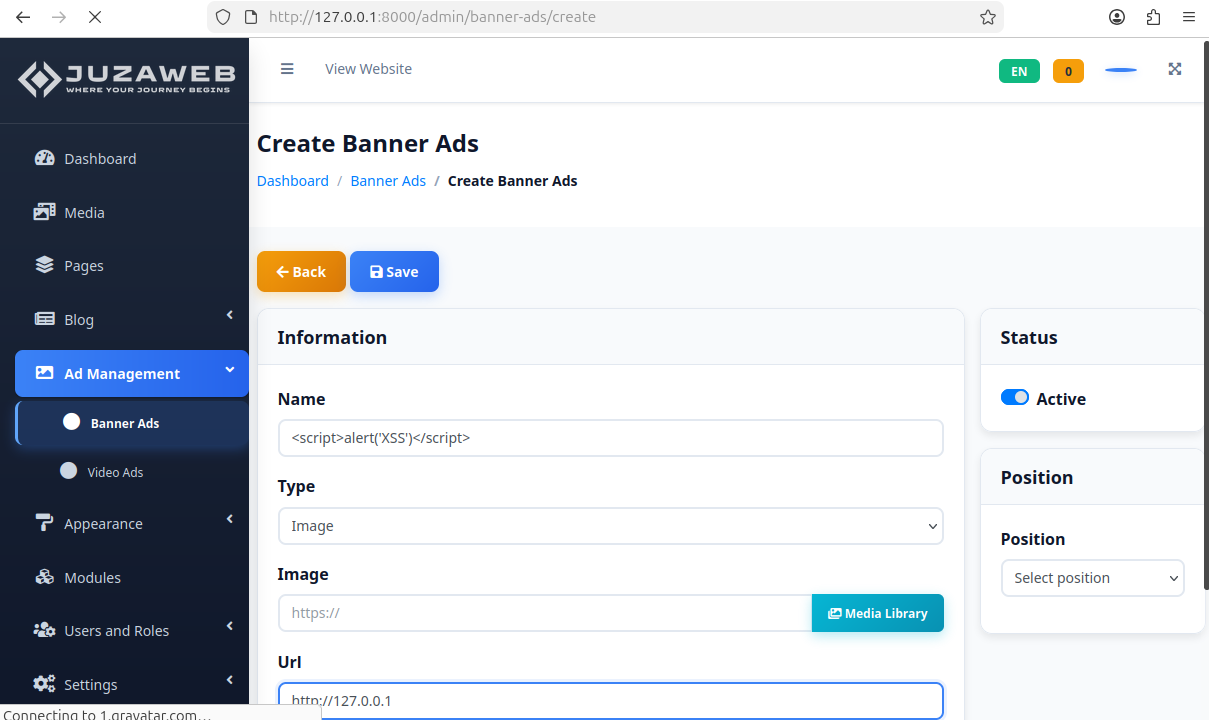 完成添加之后可以看到正在运行
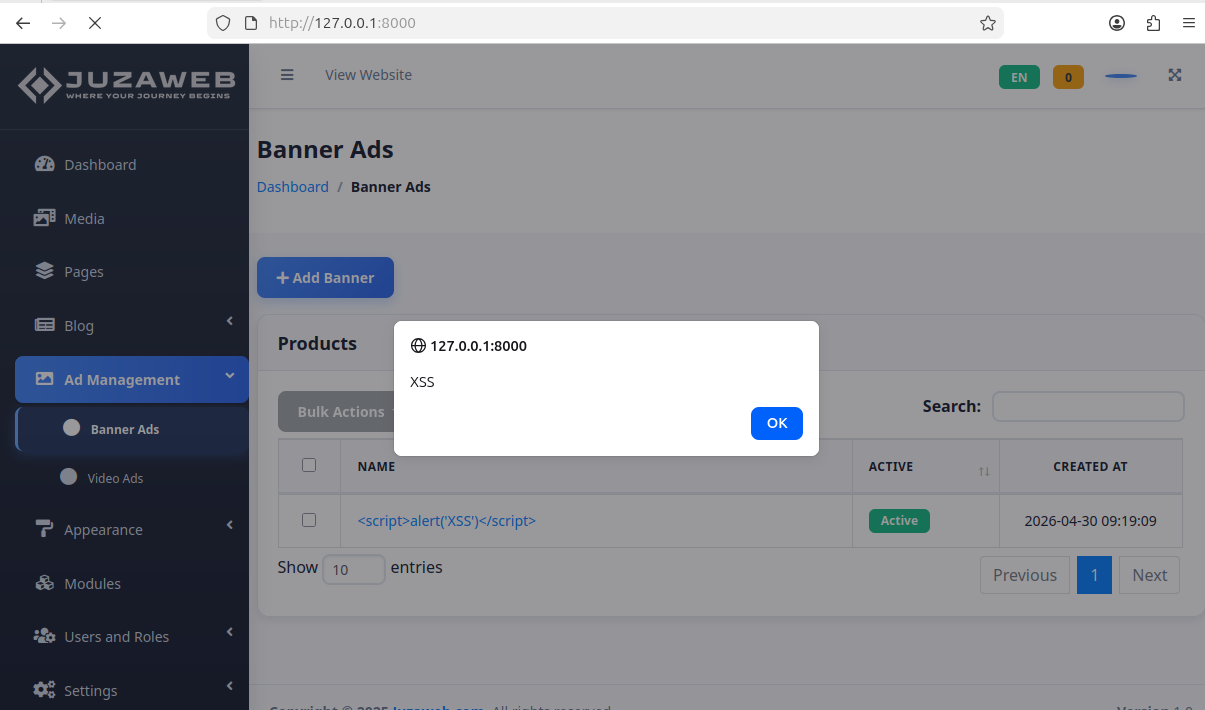
完成添加之后可以看到正在运行 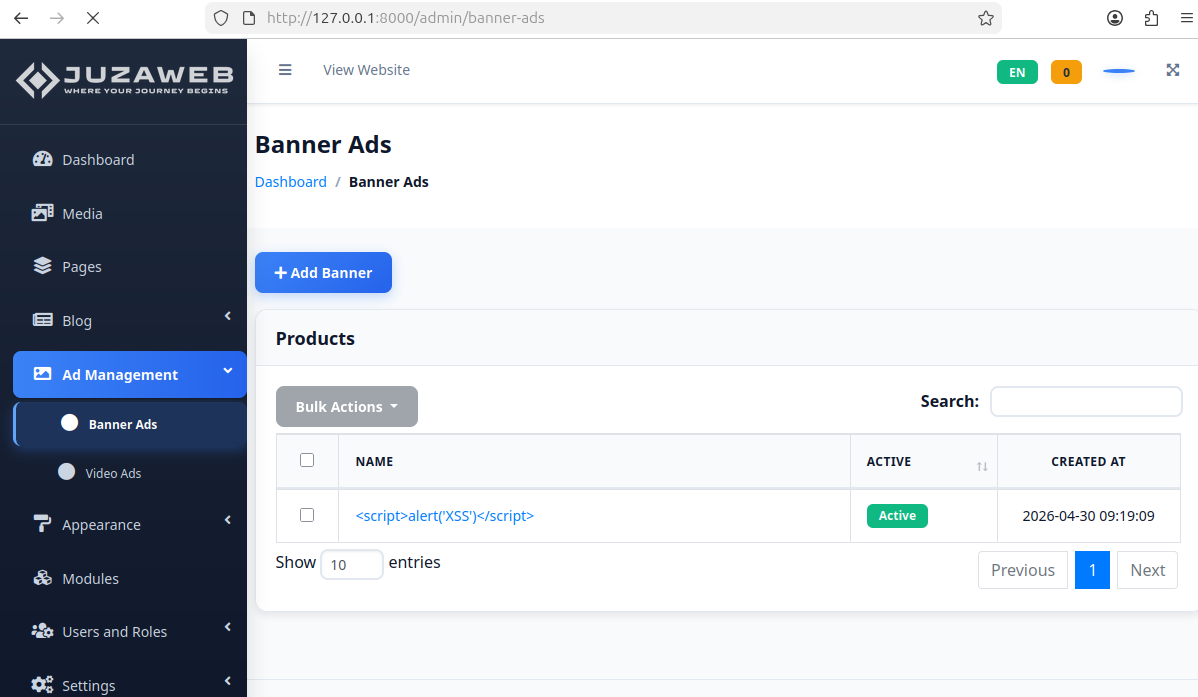 这时候返回主页就可以看到弹窗
这时候返回主页就可以看到弹窗 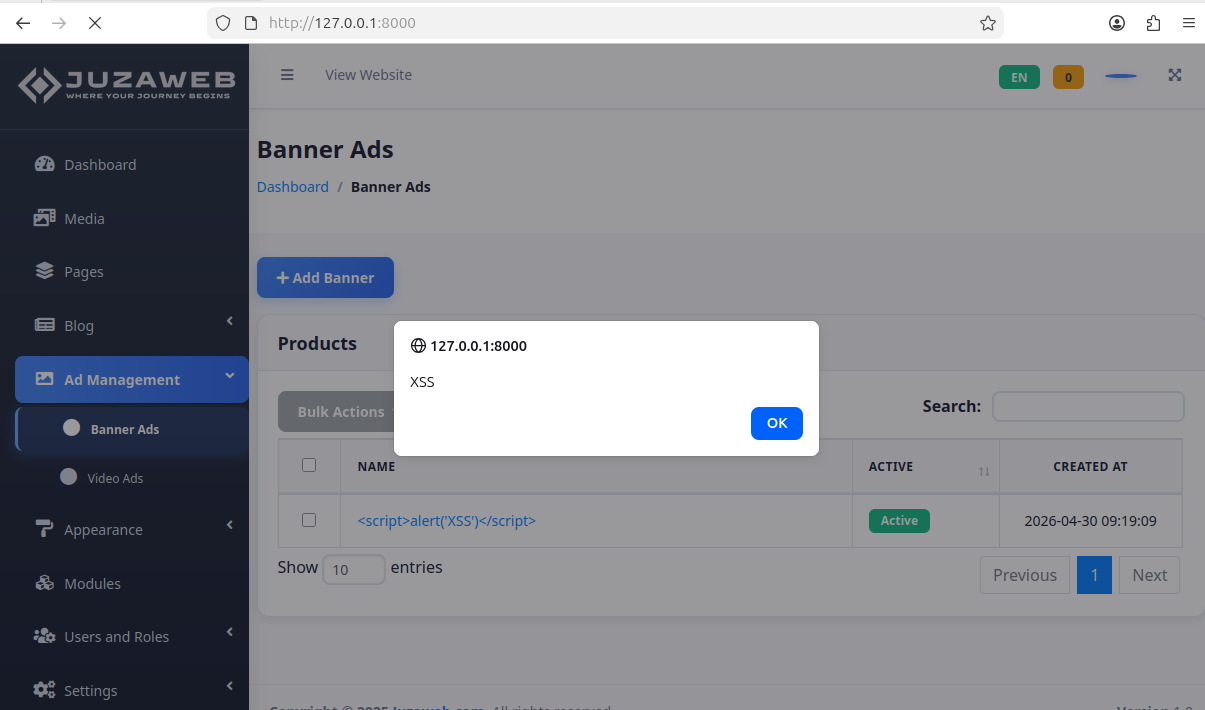
参考链接:
包含漏洞详细信息的 Gist 公开链接: https://gist.github.com/yuhuamiao/2c984b2d7f2adb90020818f9308b5862
原始概念验证代码及截图:https://github.com/yuhuamiao/CVE-2026-36358
Description:
Juzaweb CMS version 5.0.0 is vulnerable to Stored Cross-Site Scripting (XSS) in the ‘/admin/banner-ads’ component. An authenticated administrator can inject arbitrary JavaScript code into the “HTML” banner ad body. When any user (including non-authenticated visitors) accesses the homepage, the malicious script will be executed in their browser.
Affected Product: Juzaweb CMS Affected Version: 5.0.0 Vulnerability Type: Stored Cross-Site Scripting (XSS)
Proof of Concept (PoC):
First, set up the platform normally and register an account. Here, the administrator account I registered is 123@123.com / 123456.
After setting up the platform, you can see the website homepage.
Access /admin and log in.
After logging in, you will enter the admin backend dashboard.
Navigate to the /admin/banner-ads route and click “Add Banner” to go to the ad creation page.
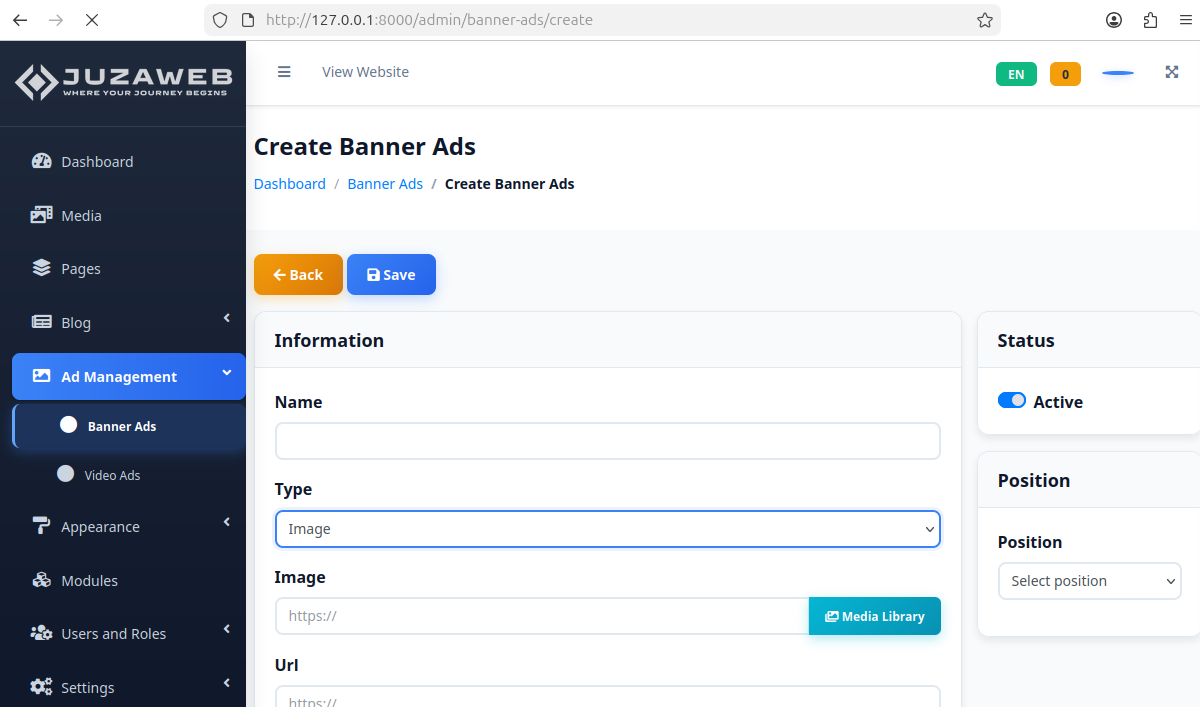
Change the Type to “HTML” and insert the malicious XSS code into the Body field.
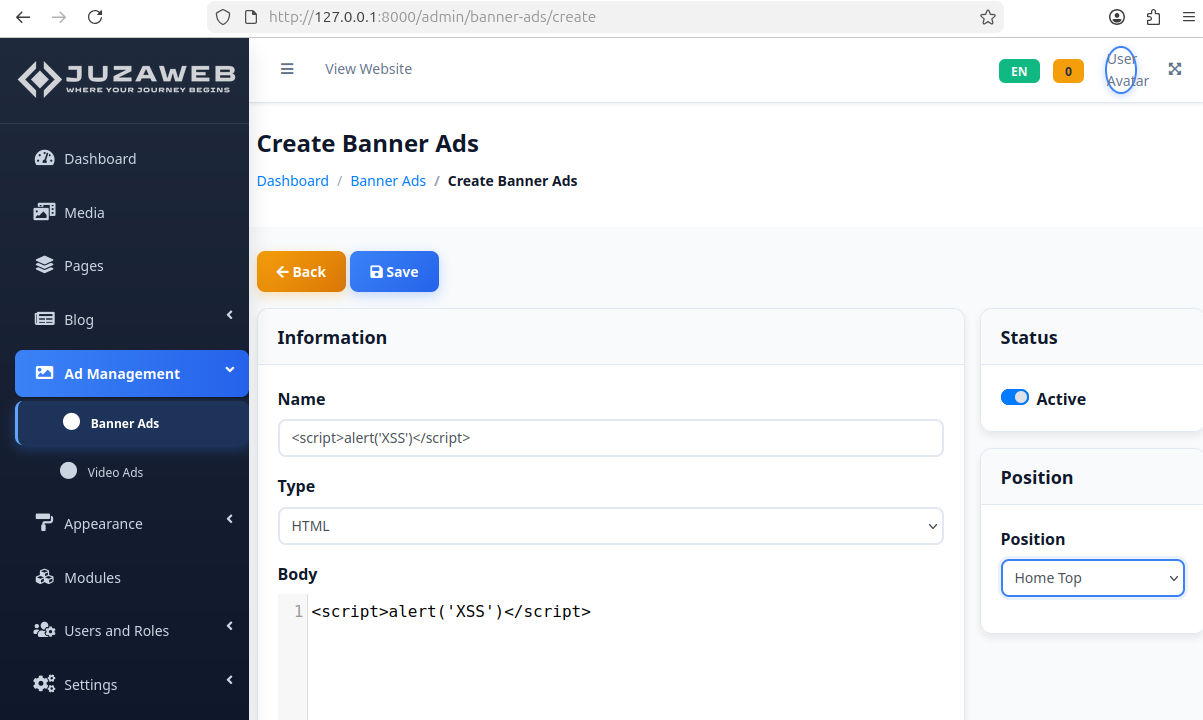
If you encounter an error like this:
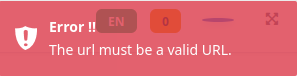
Go back to the “Image” Type and enter any URL in the URL field.
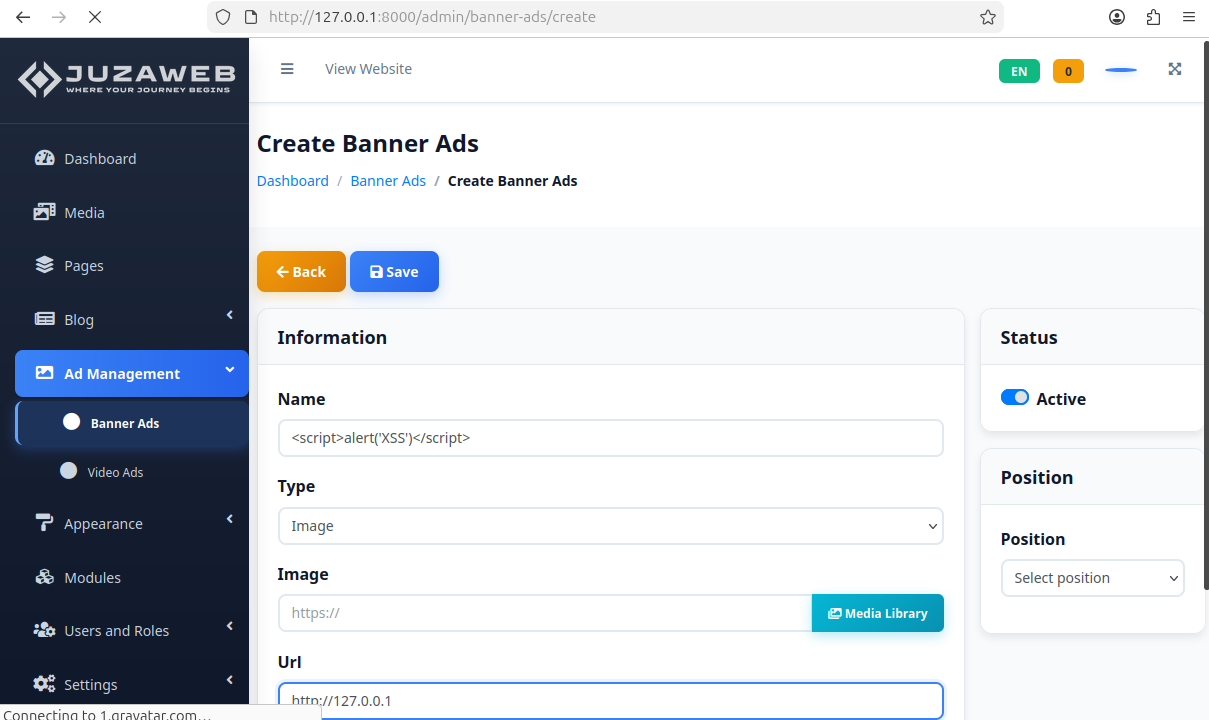
After successfully adding the ad, you can see it is active/running.
Now, return to the homepage. The alert box will pop up, demonstrating the XSS vulnerability.
Reference:
Public Gist containing detailed vulnerability information:
https://gist.github.com/yuhuamiao/2c984b2d7f2adb90020818f9308b5862Original PoC and screenshots: https://github.com/yuhuamiao/CVE-2026-36358